DoctorCaT
Basic
- Joined
- 04.08.21
- Messages
- 19
- Reaction score
- 8
- Points
- 3
The Hacker's Story:
5 years ago I could not even think about hacking something related to cryptocurrency, it seemed like a big hoax to me then. As of now, 2021, I am actively involved in hacking, testing security systems of different crypto-platforms.

Conclusion of a cyber security expert:
"Cybercrime incidents are growing year after year - there doesn't seem to be a slowdown for Internet criminals.With the advent of cryptocurrency, these cybercriminals now have new aspirations and new motives for their online criminal activity.
Moreover, the rise of cryptocurrency has led to the creation of new types of criminal activity.
Cryptojacking, Ransomware and various other such activities have a direct correlation with the growth of cryptocurrency.
Cryptocurrency traders are also a target - because some of them are the first traders to be lured by the massive price increases that cryptocurrencies have to offer.
Current cybercriminals now use tactics as simple as the old phishing techniques to steal crypto-money.
Sometimes these attacks are more advanced, such as cryptocurrency exchanges, hacked data, or extortion attacks.
Let's take a closer look at how cryptocurrency poses a threat to cybersecurity."
All the efforts of cybercrime departments go nowhere, a small group of hackers can quickly change their habitat. We all heard about the big break-ins, where are the arrests ??? why no news about the arrests of hackers ???
If anyone remembers the hack "Lurk Group" mass hack - so they were caught not during the hack, but on the withdrawal of funds: Well it's all lyrics by the author ...
Let's talk about something we can use:
Everyone knows that many countries have already adopted cryptocurrency as a major currency: in particular El Salvador:There are many services aimed at improving the ecosystem of "BITCOIN" - what does this give us? Well, at least everything!
Author's thoughts:
I do not even know why I will write further this article - people whose head works, have long earned a fortune on this. A day I write to 20 people with the question how to make money. I immediately tell them to fuck off, because this trash is not worthy of my attention.So who is this article for? Probably for myself: only in the past. Some smart person will read it and maybe discover new ideas or ways to make money.
For the rest of you: go fuck yourselves, continue discussing bullshit in your fucking chats....
So, next I'm going to write about a project which was developed by me personally:
It's about crypto loans.
I'm not going to tell you what it is and how it works.................Using a security bug in DeFi Flash Loans protocols
Flash Loan HacksIn 2017, during a DAO, decentralized autonomous organization, hack, multiple protocols were 51% attacked for the users profit.
The 51% attack happens on the blockchain network when a user can get control of most of the hash rate (over 50%) and have enough power to modify or prevent transactions from happening.
Since blockchains rely on nodes like PoW, or proof of work, it is important to disburse the nodes across as many different entities as possible to mitigate a 51% hack.
As of 2019, DeFi providers hacks are not as brutal and often not as conspicuous. Of the easiest and most common ways is to exploit vulnerabilities and platform bugs. For example, attacks on the ApeRocket (Polygon) protocol have been carried out using only flash loans through Aave and PancakeSwap (More details on the developer's blog).
Hacking Theory
Most providers of DeFi Flash Loan projects that do not use LTV are using protection systems like Plasma and NuCypher.
The problem with these systems is their complicated implementation in transactions between their networks and Etherium or Blockchain, for example, Plasma Brige allows double spending, which allows repeated withdrawals.
NuCypher allows developers to store, share and manage personal data and seeks to add an interoperable layer of security to various blockchains, where developers can grant permission to access sensitive information in a number of decentralized applications, but in practice the platform only offers secret management and dynamic access control services through Umbral, its encryption scheme, and Ursula, a network of operating nodes.
Umbral is a NuCypher encryption scheme that allows users to keep data private and share information securely.
Data owners grant decryption rights to the recipient of the data in a process run by "proxy nodes" called Ursuls, which re-encrypt the data for the recipients. (Note that proxies do not have access to the underlying data or unlock keys, they simply apply additional conditions that must be met to unlock the data).
After running diagnostics on providers such as AAVE, Fulcrum, Finside, MarkerDAO, we found out that the bug is applicable within a single transaction.
Using the method on the Finside platform:
lead-up
1.Connect the anonymity binder.We will not waste time discussing ways to anonymize the network, find out the difference between VPS and VDS, and argue about the advantages and disadvantages of RDP and VPN. If you don't have enough skills to create a stable personal security bundle, the following information is definitely not for you.
2. Buy fake IDs and get verified.
3. Buy a phone number on the Internet to receive SMS.
4. Issue credit by specifying your Blockchain, Payeer or MetaMask wallet.
5. Withdraw cryptocurrency via p2p to DEX account and disappear (using mixer).
Step by step
When registering on the platform under no circumstances use temporary or compromised email addresses, invalid phone numbers and check the spelling of the data several times. In case of any mismatches, the probability of a thorough data check increases many times over. The entire registration process is available here.Apply (link), but make sure that the payment address is correct, because that is where the loan amount will be received.
If the loan is approved, you will have 90 minutes to withdraw the funds to the wallet you specified (I used a blockchain wallet).
After receiving the funds in your purse use p2p exchange service, for example Remitano or a decent exchange office with a reputation on the site Bestchange.
Carry out an operation to change the blockchain, for example BTC - XMR to DEX wallet. If you use DEX wallet Wasabi or Samourai - connect the built-in mixer, in other cases, make a withdrawal through external mixers.
Find another device (since the system reads MAC addresses) or change the MAC using root rights and repeat the procedure for as long as there are fake ID's.
You can buy the full version of the method with active links to the platform and the possibility of online support at any stage of the attack here.
Sale of unique documents here.
Still, I wanted to talk about anonymity, let me not tell you all the subtleties in this article. I will just give you some useful tips on this topic.
More information in my telegram channel: https://t.me/joinchat/copTAJUSRh8xNDNh
I will also give some useful information, I think it will be useful for someone.

I think every one of us is wondering where to store his bitcoins, let me try to help you with choosing a wallet. Actually there are a lot of bitcoin wallets, but today we will consider only 2 Wasabi and Samurai.
Both of them are anonymous wallets, they use routing traffic through tor network by default, also there is a bitcoin mixer. They have already proven themselves, I myself use both of these wallets for about 1 year now.
official sites:
samouraiwallet.com - samurai
wasabiwallet.io - wasabi

Whonix is a Linux-based operating system focused on anonymity and security. It is designed to hide the user's IP address/location and uses the Tor network to anonymize data traffic. This means that the server being accessed and the Tor network operators cannot easily determine what sites are being visited or the physical location of the user: whonix.org

The other day I was wondering how much you can be anonymous online, and how to collect all the useful information in one place. I decided to compile a list of all the useful articles I know into one big textbook, although I can't even get 50% of all the technical literature in a telegram.
You have to understand that in order to rob a $1 million bank you have to do a tremendous amount of anonymity work, and after the robbery you have to launder the money. I will post links to useful articles that will help you in your anonymity questions.
https://anonymousplanet.org/guide.html
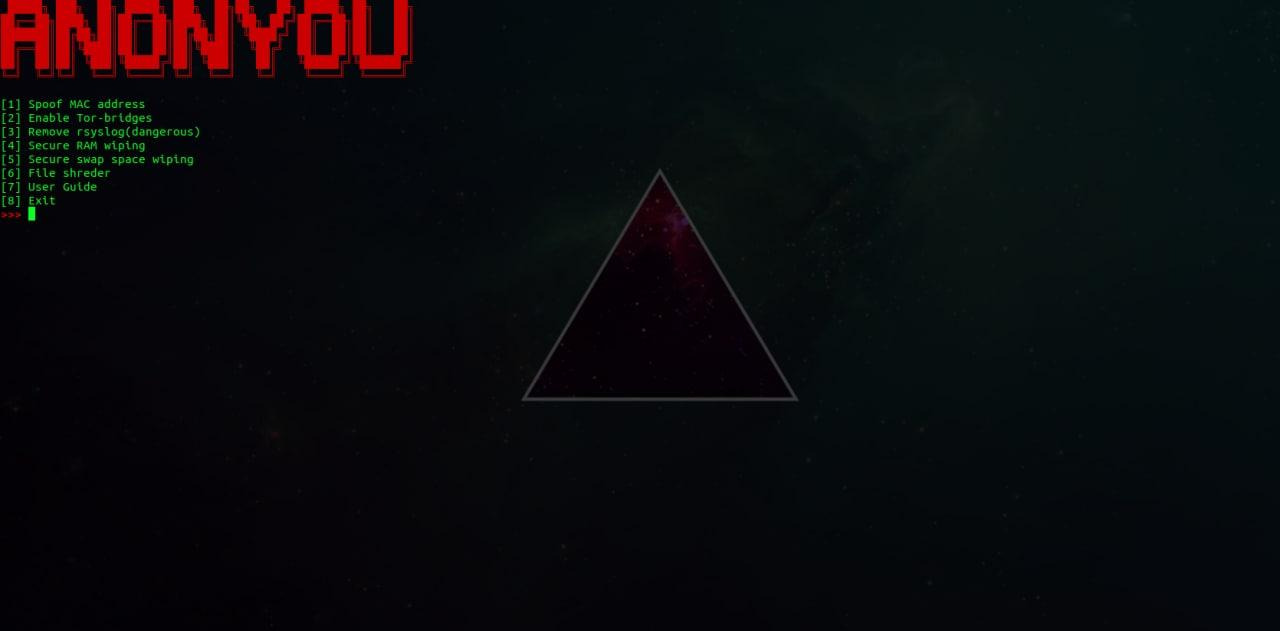
AnonYou is a free, open-source utility written in bash that allows you to quickly perform anonymization-related actions.
The following features are available :
Changing the MAC address to random or arbitrary
Redirect all traffic through TOR
RAM wiping
Swap space wipe
Securely erase files
Deleting system log
https://notabug.org/Grey_Hat_Cybersecurity/AnonYou
VPN for Monero
Since many people were interested in this question, I decided to leave this small list for VPN services that provide their services with the ability to pay with the anonymous cryptocurrency Moner?
Xeovo VPN - Key to your privacy
Silence censorship. Protect your privacy and bypass restrictions with Xeovo VPN. Starting from 2,99€/mo.

VPN Shazam - The Best Free VPN Server Address!
Welcome to VPN Shazam, Get the best free VPN server address. We provide the best best free VPN (Virtual Private Network) server address. Contact us now!

TekLan VPN | Fast, Affordable and friendly.
A small independent VPN company based in the UK. We pride ourselves on being affordable whilst offering great support! Fast, Worldwide Servers and always here!
WideVPN-Worldwide Fast Wireguard VPN Server Locations.Cheap VPN from $1.99,high speed, unlimited bandwidth
WideVPN - Providing Cheap VPN Yearly, unlimited bandwidth, unblock websites & encrypt your connection.Multi Protocols and Wireguard,Works on every major platform
 www.widevpn.com
www.widevpn.com
Home | What The Server
Blokada - the popular mobile adblocker and VPN for Android and iOS
Keep all your devices protected with Blokada content filtering and encryption.
VPN service for secure, anonymous and unrestricted internet access on all devices: fast servers, free access, download the VPN app — hidemy.name
Protect your devices and gain access to websites. Round-the-clock customer support. VPN for Windows, Android, macOS, iOS, and routers. Free trial period.

VPN for Privacy & Security | IVPN | Resist Online Surveillance
Audited, open-source VPN service with WireGuard, killswitch and tracker blocker. No logs, no false promises. Anonymous signup with 30 day money back guarantee.
Njalla
Njalla — Considered the worlds most notorious "e;Privacy as a Service"e; provider for domains, VPS' and VPNs.
The best online VPN service for speed and security | NordVPN
Online VPN service that encrypts your internet traffic and hides your IP with physical location. Upgrade your privacy and security now.
VPN for Security and Integrity
OVPN is the VPN service that makes you anonymous online. No logs, fast VPN speeds, strong encryption and an uptime guarantee of 99.5%
Anonymous VPN, Proxy & Email Services | TorGuard
Protect your identity and personal privacy with our anonymous VPN, proxy & email encryption services for individuals and businesses. All of our packages include unlimited speeds and bandwidth in 50+ countries. Get TorGuard today!
torguard.net
Free, Secure & Fast VPN Service | X-VPN
Ultra-fast, secure and stable VPN for all devices platform. Try risk-free with 30-day money-back guarantee. 24/7 live chat support.
The ones I use:
https://bitvps.com - His TOR mirror: http://bitvpsj2ojxo7faned27wmpqiss3pny7m7bptwtnegl7fswjrxwtmxid.onion
14EZXMSMTjXXvnUuM7QwyY7fohGY75rgcF
Donate(BTC)



